The operational backbone
Industrial SCADA, built for portfolios.
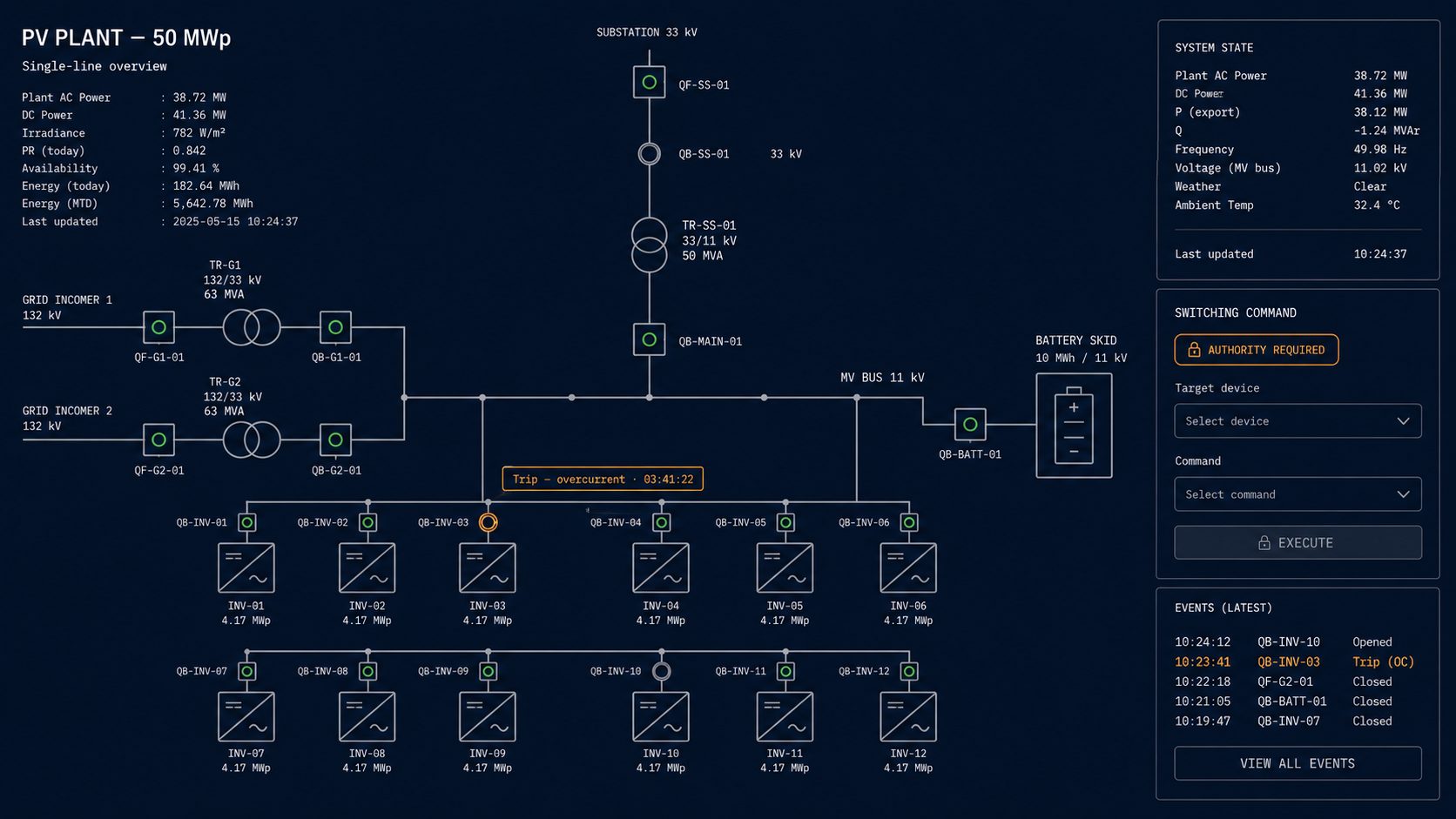
Real-time monitoring, supervisory control, and a high-resolution historian. Every site under one tenant. Every major OEM ecosystem on day one. LumeTrax® Core is the supervisory layer the operator actually drives the plant from — alarm philosophy, control authority matrix, deterministic OT boundary, all native.
Capex on the gateway hardware (sized in the questionnaire). Subscription on the software. Cloud, private, on-prem, or air-gapped.
One supervisory environment. One historian. Every site.
Core is the deterministic operational layer. Real-time data ingestion from inverters, BESS, switchgear, met stations, trackers, and DG controllers. Supervisory control of breakers and switching. One-line diagrams that mirror the as-built. Alarms with engineering-grade philosophy, not consumer-app pop-ups. A historian sized for analytics, not just last-week-in-Grafana.
Core sits where SCADA actually sits — inside the deterministic OT boundary, with control authority, interlocks, and historian native to the same software. Analytics, workflow, and assurance run above the boundary as separate modules. Each layer where it belongs.
The operator's screen, not the marketing screen
Supervisory control where the safety logic actually lives.
Operators get one-line diagrams that match the as-built single-line, breaker status that reflects field reality within sub-second latency, and supervisory commands gated by role, interlock, and audit trail. Alarms are categorised by severity, system, and consequence — not by whichever vendor screamed loudest first.
Industrial-grade, not consumer-grade
A drift in renewable monitoring over the last few years has been toward simplified, consumer-style UIs that trade supervisory depth for dashboard polish. We did the opposite. The screen the operator drives the plant from is built against industrial standards — alarm philosophy, deterministic latency, audit trail, command authority, fault tolerance. Polish is fourth-order. The first three are non-negotiable.
What Core can do — and what it deliberately can't
Authority is a configuration, not an assumption.
Every supervisory command in Core is gated by an explicit authority matrix: who can issue the command, against which asset, in which operating mode, with which interlocks active. The matrix is documented per deployment, version-controlled, and audit-logged. There is no "default-on supervisory privilege" — operator authority is configured, granted, and revocable.
Critical interlocks, safety-critical sequencing, and protective trip logic remain inside the deterministic SCADA / PLC / RTU boundary. Core issues supervisory intent across the boundary; the OT layer enforces the safety constraint. If the network link to Core fails, the on-site PLC continues to run protected operation against its locally-configured logic.
Fail-safe behaviour is explicit per deployment. Communication loss → hold last commanded state, then enter local-fallback regime after a configurable hold-down. Manual override available at the panel. Every transition logged.
Where the software meets the field
Hardened on-site or near-site, sized to the deployment.
Core ships with an industrial-grade edge gateway that handles ingestion, local supervisory functions, offline buffering during network outages, and tenant-side data normalization before sync. Hardware is sized to the deployment in the Core questionnaire — environmentally-rated, redundant-power, often dual-NIC for OT/IT segregation.
Cloud
Gateway → managed cloud region
Private cloud
Gateway → single-tenant cloud
On-prem
Gateway → customer datacentre
Air-gapped
Gateway → on-prem, no outbound connectivity
Sized to the deployment in the Core questionnaire.
Vendor-agnostic by architecture · protocol-first integration
Speak the protocols the field already speaks.
Core integrates with every major inverter, BESS, switchgear, tracker, and DG ecosystem over the protocols those ecosystems publish — so a mixed-OEM portfolio runs under one tenant without a custom-integration line item per site. New ecosystems are added when the field requires them.
Modbus TCP / RTU · IEC 61850 · SunSpec · MQTT · OPC UA · OEM APIs
Portfolio-ready from day one
One tenant. One data model. Every plant.
The tenant hierarchy is the same on every screen and every report — Client Organization → Portfolio → Plant → Subsystem → Asset → Tag/Point/Event. Add a new plant under an existing tenant and your portfolio view, your KPIs, your audit trail, and your access control update on the same login. No second instance to provision. No second contract to negotiate.
The audit trail your lender will eventually ask for
Engineering-grade alarms. A historian sized for the questions you don't know you'll be asked yet.
Alarm philosophy
Event chronology
High-resolution historian
The boundary that protects the asset
Mission-critical control stays deterministic. Always.
Supervisory control, interlocks, and safety-critical logic live inside the OT boundary — SCADA, PLC, RTU, site controller — exactly where engineering practice expects them to live. Analytics, workflow, optimization, and assurance services run above the boundary, in shared platform services. The boundary is drawn into the architecture, not into a slide.
What happens between contract signature and first operator login
Sized to the asset. Documented per deployment.
| Stage | What happens | Typical duration |
|---|---|---|
| 1. Scoping | Core questionnaire — plant technical scope, control authority, integration map, deployment shape, identity & access, support tier | 2–4 weeks |
| 2. Engineering | As-built capture, alarm philosophy configuration, authority matrix, OT/IT segmentation design, gateway hardware sizing | 4–8 weeks |
| 3. Field commissioning | Gateway install, protocol commissioning per asset, control-loop verification, alarm-and-event sign-off | 2–6 weeks per site |
| 4. Operator hand-off | Operator training, runbook delivery, support tier activation | 1–2 weeks |
Site-dependent. Standard utility-scale single-OEM plants with documented register maps commission inside weeks. Mixed-OEM brownfield assets with undocumented field devices take longer — the questionnaire surfaces those variables before commercials are agreed.
Pricing
Core software subscription. Edge hardware capex. Both sized to the deployment.
Core ships in two parts. The software is subscribed per plant, per tenant, with public starting prices below. The edge hardware — gateway controller, environmentally rated, sized to the deployment — is capex'd to the project the same way any industrial control hardware is.
| Tier | Software starting price | Edge hardware capex | Suited for |
|---|---|---|---|
| Core Control | from $2,500 / mo | sized in questionnaire | Single utility-scale plant or small portfolio. Real-time monitoring and supervisory control with the standard alarm and historian package. |
| Core Command | from $5,500 / mo | sized in questionnaire | Multi-plant operations with redundancy, advanced control authority, and richer integration scope. |
| Enterprise | quotation | sized in questionnaire | Portfolio scale, custom integrations, private deployment, advanced identity, regulated-environment requirements. |
Indicative starting points only. Final pricing depends on plant architecture, integration scope, deployment model, support level, and portfolio size. Edge-hardware capex sized in the Core questionnaire — not anchored on the price page.
Frequently asked questions
- No. The tenant hierarchy and tag model are documented and exportable. A LumeTrax tenant can stand up beside an existing historian during a transition, and a customer who later moves off LumeTrax leaves with their historian data intact.
- Yes. Cloud, private cloud, on-prem, and air-gapped operation are first-class deployment shapes. The deployment topology is reviewed in the Core questionnaire as part of the quotation.
- Site-dependent. A standard utility-scale single-OEM plant with documented register maps and accessible communication infrastructure typically commissions inside weeks. Mixed-OEM brownfield assets with undocumented field devices take longer — the questionnaire surfaces those variables before commercials are agreed.
- The integration approach is protocol-first (Modbus, IEC 61850, SunSpec, OPC UA, OEM APIs). Every major ecosystem is addressed; the questionnaire confirms scope per-asset. New ecosystems are added when the field needs them.
- Yes — this is a first-order requirement. Owner, operator, EPC, and contracted O&M can all be granted scoped access (read, write, supervisory, audit) within the same tenant, with full audit trail per actor.
- The on-site PLC / RTU continues to run protected operation against its locally-configured logic. Core fails safe to a defined fall-back regime — typically a hold-last-commanded-state followed by entry into local-fallback after a configurable hold-down. Mission-critical control is unaffected because it never depended on Core to stay safe.
- A change in subscription entitlement, not a new deployment. Same platform, same tenant, same data model unlocks additional capability.
Core is the foundation. The other modules sit on top.